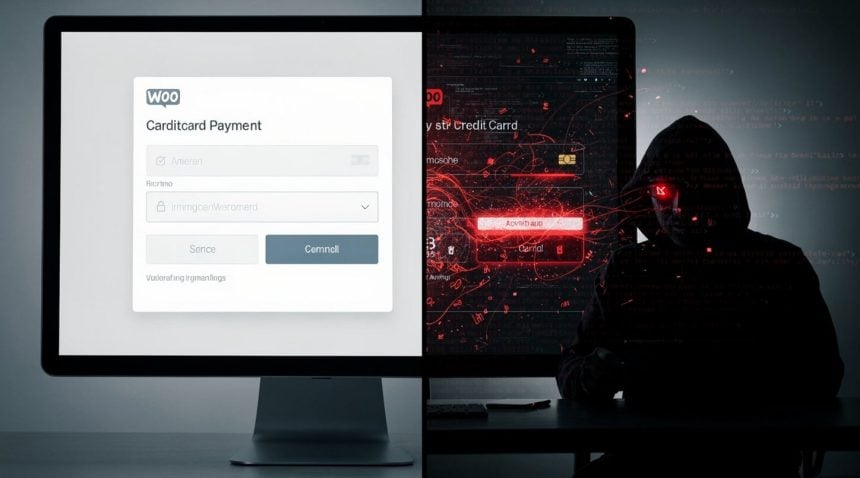
Right now, as customers enter their credit card details on thousands of WooCommerce storefronts, attackers are injecting malicious JavaScript into checkout pages to capture that payment data in real time.
The threat is immediate and widespread. A critical vulnerability in the Funnel Builder plugin for WordPress has come under active exploitation this week, according to security firm Sansec. The flaw allows attackers to inject malicious code directly into WooCommerce checkout pages—the exact moment when customers are most vulnerable, entering sensitive payment information they believe is secure.
- The Attack Scale: WooCommerce powers 42% of all online stores globally, making this vulnerability a massive attack surface.
- The Stealth Method: JavaScript injection captures payment data invisibly during checkout with no customer awareness.
- The Timing Risk: Active exploitation is happening now while stores remain unpatched and vulnerable.
Funnel Builder is a WordPress plugin used by online merchants to create sales funnels and optimize checkout experiences. The vulnerability currently lacks an official CVE identifier, meaning the broader security community is still cataloging its scope. But Sansec’s discovery confirms the exploit is not theoretical: it is happening now, in the wild, across active stores.
The attack method is straightforward and effective. By exploiting the plugin flaw, hackers inject JavaScript code into the live checkout environment. This injected code runs invisibly in the customer’s browser, capturing payment card details, billing addresses, and other sensitive checkout data as they are entered. The customer sees nothing amiss. The checkout appears to process normally. But the attacker has already harvested the data.
How Does Plugin Exploitation Scale Payment Data Theft?
This is payment-data skimming at scale—a technique that has plagued e-commerce for years, but one that typically required attackers to compromise individual store servers or payment processors. The Funnel Builder vulnerability democratizes the attack: any attacker who understands how to exploit this specific flaw can target hundreds or thousands of stores simultaneously, without needing to breach each one individually.
• WordPress plugins are often developed by small teams with limited security resources
• A single flaw in a widely-used plugin creates massive attack surfaces
• Research shows active exploitation of WordPress plugin vulnerabilities is increasingly common
The scope of exposure is still being assessed. Sansec published details of the activity this week, but the full number of affected stores and compromised transactions has not been disclosed. WooCommerce powers approximately 42% of all online stores globally, and Funnel Builder is a popular choice among merchants using WooCommerce. The potential scale is enormous.
Why Does This Attack Mirror Historical Data Harvesting?
What makes this incident structurally significant is not just the theft itself, but the invisibility of the mechanism. Customers have no way to know their data has been harvested. Store owners may not immediately realize they have been compromised. The attacker operates in the gap between user action and transaction completion—a gap that has historically been the hardest to secure.
This mirrors the logic that made Cambridge Analytica’s data harvesting so effective: the extraction happened silently, at scale, without the knowledge or consent of those being profiled. In CA’s case, behavioral data was harvested through Facebook apps and third-party integrations. Here, payment data is harvested through a trusted plugin, during a moment of high trust. The structural parallel is stark: both rely on a compromised intermediary to access sensitive information at the moment of user vulnerability.
What Should Store Owners Do Immediately?
Store owners using Funnel Builder should treat this as urgent. The plugin should be considered unsafe until a patch is released and verified. Sansec’s disclosure is a public warning, not a full remediation. Merchants should check their transaction logs for suspicious activity, particularly any transactions that processed but show signs of fraud or chargeback patterns. If you operate a WooCommerce store using Funnel Builder, disable the plugin immediately and consider switching to an alternative checkout solution until a security update is available.
• Disable Funnel Builder plugin on all WooCommerce stores immediately
• Review transaction logs for unusual patterns or chargeback spikes
• Consider alternative checkout solutions until patches are verified
For customers, the risk is more diffuse. If you have made a purchase on a WooCommerce store powered by Funnel Builder in recent weeks, your payment information may have been captured. Monitor your credit card statements closely for unauthorized charges. Consider placing a fraud alert with your credit card issuer. If you see suspicious activity, report it immediately.
What Does This Reveal About E-commerce Security?
The vulnerability underscores a persistent weakness in the WordPress ecosystem: plugins are often developed and maintained by small teams with limited security resources. A single flaw in a widely-used plugin can create a massive attack surface. This pattern has been documented in supply chain attacks across different software ecosystems, where trusted intermediaries become the weakest link.
Sansec’s discovery is a reminder that the weakest link in e-commerce security is often not the payment processor or the bank—it’s the merchant’s own software stack. Security research demonstrates that vulnerabilities in widely-deployed plugins create opportunities for automated exploitation at unprecedented scale.
The critical question now is speed of patching. How quickly will Funnel Builder’s developers release a fix? How quickly will store owners apply it? Until then, attackers will continue exploiting this vulnerability. The window of active exploitation may last days or weeks. Every transaction processed through a vulnerable store during that window is at risk.