Zero-knowledge encryption sits at the center of a growing regulatory divide between privacy advocates and law enforcement agencies worldwide. While the technology promises unprecedented user privacy, governments are pushing for “lawful access” requirements that could fundamentally undermine its core security guarantees. This tension will define the next phase of digital rights legislation across jurisdictions.
- The Technical Impossibility: True zero-knowledge systems make data mathematically inaccessible even to service providers under court orders.
- The Market Split: Signal threatens UK exit while WhatsApp maintains encryption backdoors through cloud backup defaults.
- The Enforcement Reality: ProtonMail has complied with 6,932 law enforcement requests since 2017, providing only metadata due to technical limitations.
How Does Zero-Knowledge Encryption Actually Work?
Zero-knowledge encryption represents a cryptographic approach where service providers cannot access user data, even when compelled by court orders or government requests. Unlike traditional encryption where companies hold decryption keys, zero-knowledge systems generate encryption keys locally on user devices, making the data mathematically inaccessible to the service provider.
The distinction matters legally. When Apple fought the FBI’s demand to unlock the San Bernardino shooter’s iPhone in 2016, the company argued it would need to create new software to bypass its security. With true zero-knowledge systems, providers can truthfully claim technical impossibility—they genuinely cannot access encrypted data, regardless of legal compulsion.
Companies like Signal, ProtonMail, and Tresorit have built business models around this technical guarantee. Signal’s servers store only encrypted messages that the company cannot decrypt. ProtonMail encrypts emails using keys generated in the browser, making even targeted surveillance technically challenging.
Why Are Governments Targeting Encrypted Communications?
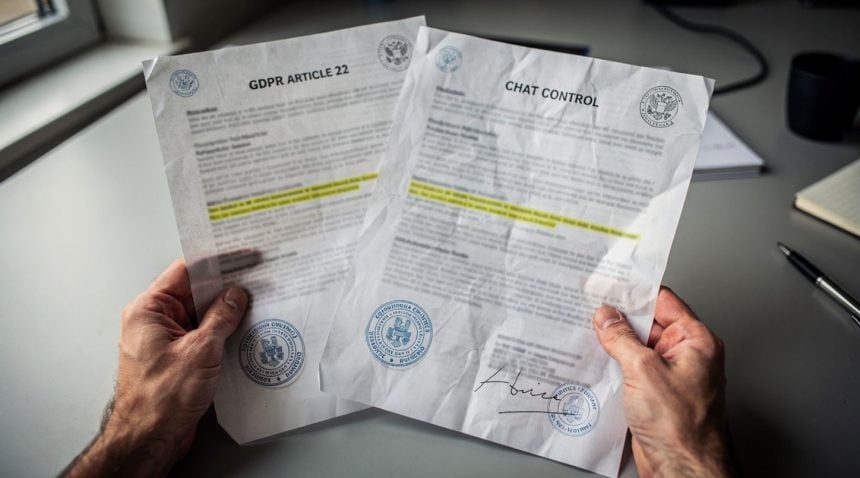
The EU’s Digital Services Act and proposed Chat Control regulation create direct conflicts with zero-knowledge encryption. Article 7 of the proposed Chat Control would require platforms to detect and report child sexual abuse material (CSAM) in private communications. For zero-knowledge systems, this creates an impossible mandate: scan content you cannot access.
EU lawmakers have proposed “client-side scanning” as a technical solution—software that scans messages before encryption. Privacy researchers uniformly reject this approach. A 2021 letter signed by over 100 cryptography experts warned that client-side scanning “would be a gift to malicious actors” and “unquestionably harmful to privacy and security.”
• March 2024: UK’s Ofcom must publish technical standards for content scanning
• Late 2024: Online Safety Act enforcement begins
• 2025-2026: EU Chat Control regulation faces member state opposition
The UK took a more direct approach. The Online Safety Act, which received Royal Assent in October 2023, grants Ofcom power to require platforms to use “accredited technology” to identify harmful content. Section 110 explicitly allows Ofcom to mandate content scanning, even in encrypted communications.
Signal responded by threatening to exit the UK market entirely. The company’s president, Meredith Whittaker, stated flatly: “We will not undermine the encryption that keeps Signal users safe.” This isn’t posturing—Signal withdrew from Iran in 2021 rather than comply with censorship requirements.
The American Exception
The United States presents a regulatory puzzle. The Fourth Amendment and strong First Amendment protections have historically shielded encryption from direct government bans. The Communications Assistance for Law Enforcement Act (CALEA) requires telecom providers to enable wiretapping but explicitly exempts “information services” like messaging apps.
However, the EARN IT Act, reintroduced in Congress in 2023, would eliminate Section 230 protections for platforms that don’t follow “best practices” for preventing CSAM. The National Center for Missing & Exploited Children could define these practices, potentially requiring encryption backdoors without explicitly mandating them.
What’s Really Happening in the Encrypted Messaging Market?
Regulatory pressure has created a two-tier market for encrypted messaging. Consumer-focused platforms like WhatsApp and Telegram market themselves as “end-to-end encrypted” while maintaining architecture that enables some form of lawful access. WhatsApp encrypts messages in transit but stores unencrypted backups in iCloud and Google Drive by default. Telegram doesn’t even enable end-to-end encryption by default in group chats.
This creates what privacy researchers call “compliance theater”—the appearance of strong encryption with built-in workarounds for government access. The approach satisfies neither privacy advocates nor law enforcement agencies, but allows companies to operate across multiple jurisdictions without direct confrontation.
True zero-knowledge providers face a harder choice. ProtonMail, based in Switzerland, has handed over limited user data to European law enforcement 6,932 times since 2017, according to its transparency reports. However, the company can only provide metadata—IP addresses and timestamps—not message content.
The Economics of Privacy
Zero-knowledge encryption creates unusual business incentives. Companies cannot monetize user data they cannot access, pushing providers toward subscription models rather than advertising. ProtonMail charges €48 annually for its basic plan. Signal relies entirely on donations, receiving $105 million from the Freedom of the Press Foundation and individual donors in 2021.
This economic reality limits zero-knowledge adoption. Free, ad-supported services dominate messaging markets precisely because they can extract value from user data. True privacy becomes a premium product, available primarily to users willing and able to pay for it.
How Do Governments Actually Enforce Encryption Bans?
Governments have discovered that banning encryption and enforcing those bans are entirely different challenges. Turkey blocked access to ProtonMail and other encrypted services in 2022, but tech-savvy users simply route around restrictions using VPNs and mirror sites.
The Russian Federal Security Service (FSB) has demanded encryption keys from messaging services since 2017. Telegram initially refused and faced intermittent blocking. The company eventually reached an accommodation with Russian authorities—not by providing encryption keys, but by agreeing to remove channels that authorities deemed extremist.
This pattern repeats globally. Authoritarian governments discover that destroying specific platforms is easier than eliminating encryption entirely. Blocking individual services becomes a form of selective enforcement, pressuring companies to accept content moderation demands in exchange for market access.
• According to research published in IEEE Xplore, zero-knowledge proofs provide mathematically verifiable security guarantees in next-generation networks
• A 2026 Frontiers study confirms that quantum-resistant cryptography maintains zero-knowledge security properties
• Academic analysis demonstrates that client-side scanning fundamentally compromises zero-knowledge architectures
The Jurisdiction Shopping Problem
Zero-knowledge encryption providers have become experts in regulatory arbitrage. Signal operates from the United States, relying on First Amendment protections. ProtonMail chose Switzerland for its strong privacy laws and federal court system. Tutanota operates from Germany, accepting GDPR compliance burdens in exchange for EU market access without broader content scanning requirements.
This jurisdiction shopping creates enforcement gaps that frustrate regulators. The EU’s Digital Services Act requires platforms with over 45 million EU users to comply with content moderation rules, but encrypted platforms can argue they lack technical capacity to moderate content they cannot access.
The regulatory environment has also created unexpected connections to broader government data surveillance programs, as law enforcement agencies seek alternative methods for accessing communications data when encryption blocks traditional intercept capabilities.
What Technical Solutions Are Being Developed?
The UK’s Online Safety Act becomes the first major test case for mandatory encryption breaking. Ofcom must publish technical standards for content scanning by March 2024, with enforcement beginning in late 2024. Signal’s threat to exit the UK market will face its first real test.
The EU faces its own moment of truth with Chat Control. After fierce opposition from digital rights groups and several EU member states, the regulation has stalled in committee. Germany and the Netherlands have signaled opposition to client-side scanning requirements, potentially forcing compromise language that creates encryption exemptions.
In the United States, the Supreme Court will likely determine encryption’s constitutional status within the next five years. Several circuit courts have recognized a First Amendment right to publish encryption software, but no high court has ruled on government mandates to weaken encryption for law enforcement access.
The Technical Arms Race
Cryptography researchers are developing new techniques designed to satisfy both privacy and regulatory requirements. Homomorphic encryption allows computation on encrypted data without decrypting it, potentially enabling CSAM detection while preserving message privacy. Private set intersection protocols could allow platforms to check messages against databases of known illegal content without revealing message contents to human reviewers.
However, these technical solutions remain experimental and computationally expensive. They also require trust in the institutions maintaining content databases—a trust that privacy advocates argue is precisely what zero-knowledge encryption exists to eliminate.
• Cryptography experts warn that any compromise to zero-knowledge architecture creates systemic vulnerabilities
• Technical solutions like homomorphic encryption remain 10-100x more computationally expensive than current methods
• Regulatory compliance through technical backdoors historically leads to exploitation by malicious actors
The regulatory pressure on zero-knowledge encryption reflects a broader collision between technological capability and state power. Governments that have always possessed the theoretical ability to monitor private communications now face mathematical barriers they cannot overcome through legal authority alone. How democratic societies resolve this tension will determine whether strong privacy remains available to ordinary users or becomes a privilege reserved for those with sufficient technical knowledge to circumvent regulatory restrictions.
The next 18 months will provide definitive answers. Either zero-knowledge encryption providers will find ways to operate within new regulatory frameworks, or they will face the choice between compromising their core security guarantees and withdrawing from major markets entirely. The outcome will establish whether true privacy remains compatible with regulated digital services in democratic societies.