A security researcher demonstrated a complete bypass of the European Union’s flagship age-verification system in just two minutes, raising urgent questions about whether the bloc’s most ambitious child-protection initiative can actually work as designed.
The EU’s age-verification framework was built to prevent minors from accessing adult content, gambling sites, and other age-restricted services across member states. The system represents a centerpiece of European digital regulation, embedded in laws like the Digital Services Act. But the speed at which researchers cracked it suggests the infrastructure may have fundamental architectural weaknesses that no amount of patching can fix.
- The Bypass Speed: Security researchers defeated the EU’s age-verification system in approximately 120 seconds using basic technical knowledge.
- The Design Flaw: The decentralized architecture creates security gaps that attackers can exploit without sophisticated tools or insider access.
- The Regulatory Impact: Platforms under the Digital Services Act must now choose between invasive verification methods or ineffective child protection.
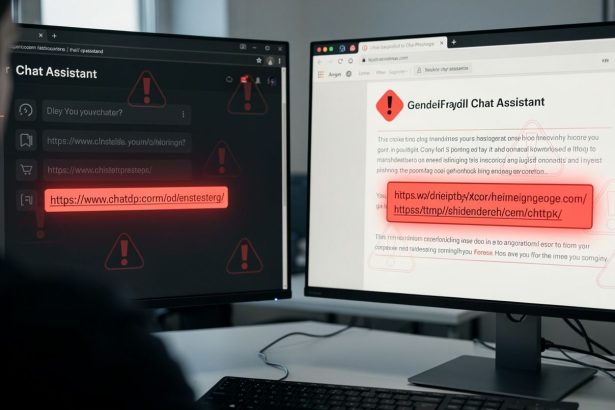
The vulnerability was discovered and demonstrated by security researchers who showed that the app’s core verification mechanism could be defeated in approximately 120 seconds. The researchers did not need sophisticated tools, insider access, or months of analysis. The attack required only basic technical knowledge and straightforward circumvention techniques. This ease of bypass is particularly damaging because age verification is supposed to function as a hard security boundary—something that, by definition, should be difficult or impossible to cross without legitimate credentials.
The specifics of how the researchers achieved the bypass were documented in their findings, though the exact technical method was not detailed in initial reporting. Research on cybersecurity vulnerabilities shows that identifying system weaknesses often requires understanding both the technical architecture and potential attack vectors. What matters is the implication: if trained security researchers can crack it in two minutes, so can determined teenagers or bad actors seeking to exploit the system for profit or harm.
Why Did the EU’s Decentralized Approach Fail?
This discovery arrives at a critical moment for EU digital regulation. The bloc has staked significant political capital on the idea that technology can be designed, regulated, and deployed to protect children while respecting privacy and avoiding mass surveillance. Age verification sits at the intersection of all three tensions. It must work reliably to protect minors. It must not require collecting and storing vast biometric or identity databases that create honeypots for hackers. And it must not become a backdoor for governments or corporations to track users.
The EU’s approach attempted to thread this needle by building a decentralized system where age verification could happen without a central authority storing everyone’s personal data. But the two-minute crack suggests the decentralized architecture itself may be the problem—that distributing the verification logic across multiple endpoints without a strong central security model creates gaps that attackers can exploit.
• Age verification systems must function as “hard security boundaries” that resist bypass attempts
• Decentralized architectures distribute verification logic across multiple endpoints
• Each endpoint represents a potential attack vector for determined users
What Does This Mean for Platform Compliance?
The implications ripple across Europe’s digital landscape. Platforms subject to the Digital Services Act must now implement age verification or face significant fines. Many have already begun rolling out systems. If the primary technical standard can be bypassed in two minutes, then either platforms will need to implement much more invasive verification methods—such as requiring government ID scans or biometric data—or they will face a choice between regulatory compliance and actually protecting children.
The research also raises questions about the EU’s testing and approval process for such systems. Age-verification technology was supposed to be vetted before deployment. Yet security researchers found the flaw quickly and without special access, suggesting either the vetting process was insufficient or the flaw emerged after approval.
How Should Parents and Users Respond?
For individual users and parents, the discovery underscores a hard truth: technical systems alone cannot enforce age restrictions. A determined minor can bypass the app. A bad actor can use the same techniques to access services they shouldn’t. The security of age-restricted content depends not just on the technology but on the broader ecosystem of enforcement, monitoring, and consequences.
• Age verification systems face the same fundamental challenges as other security boundaries
• Vulnerability research demonstrates that unattended verification systems are particularly susceptible to bypass attempts
• Effective child protection requires combining technical measures with education and oversight
What Are the EU’s Options Moving Forward?
The EU now faces a decision. It can attempt to patch the specific vulnerability researchers found, but that may only delay the inevitable—other researchers will likely find new bypasses in a system with fundamental design flaws. Alternatively, it can acknowledge that the current approach to decentralized, privacy-preserving age verification may not be technically feasible at the scale required, and pivot to a different model.
That pivot could mean accepting more invasive verification methods, which would trade child safety for privacy. It could mean accepting that some age-restricted content will remain accessible to minors despite regulatory efforts. Or it could mean investing in entirely new technical approaches that haven’t yet been invented.
The challenge extends beyond Europe. Other jurisdictions watching the EU’s approach to privacy-preserving regulation must now grapple with the same fundamental tension: how to protect children online without creating surveillance infrastructure that undermines the privacy rights the regulations were designed to preserve.
For now, the two-minute crack stands as a stark reminder that good intentions and well-designed regulations cannot overcome fundamental technical limitations. The EU’s age-verification system was meant to be a model for the world. Instead, it may become a cautionary tale about the gap between regulatory ambition and technical reality.